Railway Cybersecurity Controls That Reduce Signaling Downtime
Lead Author
Published
Views:
As digital interlocking, remote diagnostics, and networked control systems become standard across modern rail operations, railway cybersecurity is now inseparable from safety, availability, and compliance. Strong controls do more than block attacks. They reduce signaling downtime, limit fault propagation, protect operational integrity, and support resilient performance across high-speed, metro, freight, and cross-border rail networks.
What does railway cybersecurity really protect in signaling environments?

Railway cybersecurity protects the digital systems that keep trains separated, routes aligned, and operations visible. In signaling, the priority is not only data confidentiality. It is safe availability.
Key assets include interlockings, wayside controllers, RBC platforms, SCADA links, axle counter interfaces, maintenance laptops, and remote access gateways. Each connection can affect uptime.
In modern architecture, one vulnerable support system may impact dispatching, diagnostics, or failover functions. That is why railway cybersecurity must extend beyond the data center.
For advanced transportation programs, this also aligns with broader resilience expectations seen in aerospace-grade engineering. Critical systems need traceability, segregation, controlled change, and recovery discipline.
Why signaling downtime is a cybersecurity issue
Not every outage is a cyberattack. Yet weak cyber controls often turn small faults into major service disruption. A compromised workstation, misconfigured firewall, or unverified software update can halt signaling functions.
- Loss of visibility between control center and field devices
- Delayed route setting or train movement authority
- Extended recovery because logs and backups are incomplete
- Service restrictions caused by uncertain system state
Which railway cybersecurity controls reduce signaling downtime most effectively?
The most effective controls are the ones that reduce blast radius, speed fault isolation, and preserve safe fallback. Technical depth matters, but operational fit matters more.
1. Network segmentation by safety and function
Separate signaling, maintenance, corporate IT, and third-party service domains. Use tightly defined conduits, allowlists, and one-way data paths where practical.
Segmentation limits lateral movement. It also simplifies troubleshooting because teams can isolate an affected zone without freezing the whole network.
2. Secure remote access with strict session control
Remote support is common in railway cybersecurity programs, but unmanaged access raises outage risk. Require multifactor authentication, approval workflows, session recording, and time-limited credentials.
Access should be brokered, not direct. Vendors and engineers should never land inside critical signaling zones without inspection and logging.
3. Asset inventory and configuration baselines
You cannot defend what you cannot identify. Maintain a live inventory of devices, firmware, operating systems, ports, dependencies, and approved configurations.
When downtime occurs, accurate baselines shorten mean time to recovery. Teams can compare a failed state against the approved state immediately.
4. Patch governance and compensating controls
Rail systems cannot always patch quickly. Validation windows, certification impact, and service constraints are real. Railway cybersecurity therefore depends on governance, not patching alone.
Where patches are delayed, use compensating controls such as application allowlisting, jump hosts, protocol filtering, removable media control, and tighter monitoring.
5. Backup, restore, and offline recovery testing
A backup is useful only if restore works under pressure. Test images, logic files, configuration sets, and historian recovery in realistic outage scenarios.
For railway cybersecurity, offline and immutable copies are especially important. They help recover from ransomware and corrupted engineering files.
Where do rail organizations usually get railway cybersecurity wrong?
Many programs focus on compliance paperwork first and operational behavior later. That creates a false sense of maturity. Signaling uptime depends on controls that function during real incidents.
Common mistakes that increase downtime
- Flat networks connecting diagnostics and safety-adjacent systems
- Shared accounts on engineering workstations
- Uncontrolled USB devices and portable tools
- No tested recovery plan for signaling configuration loss
- Monitoring tuned for IT malware, not OT protocol anomalies
- Supplier access retained after project completion
Another frequent error is treating legacy equipment as untouchable. Older devices may be hard to modify, but they can still be shielded through zoning, gateways, and procedural control.
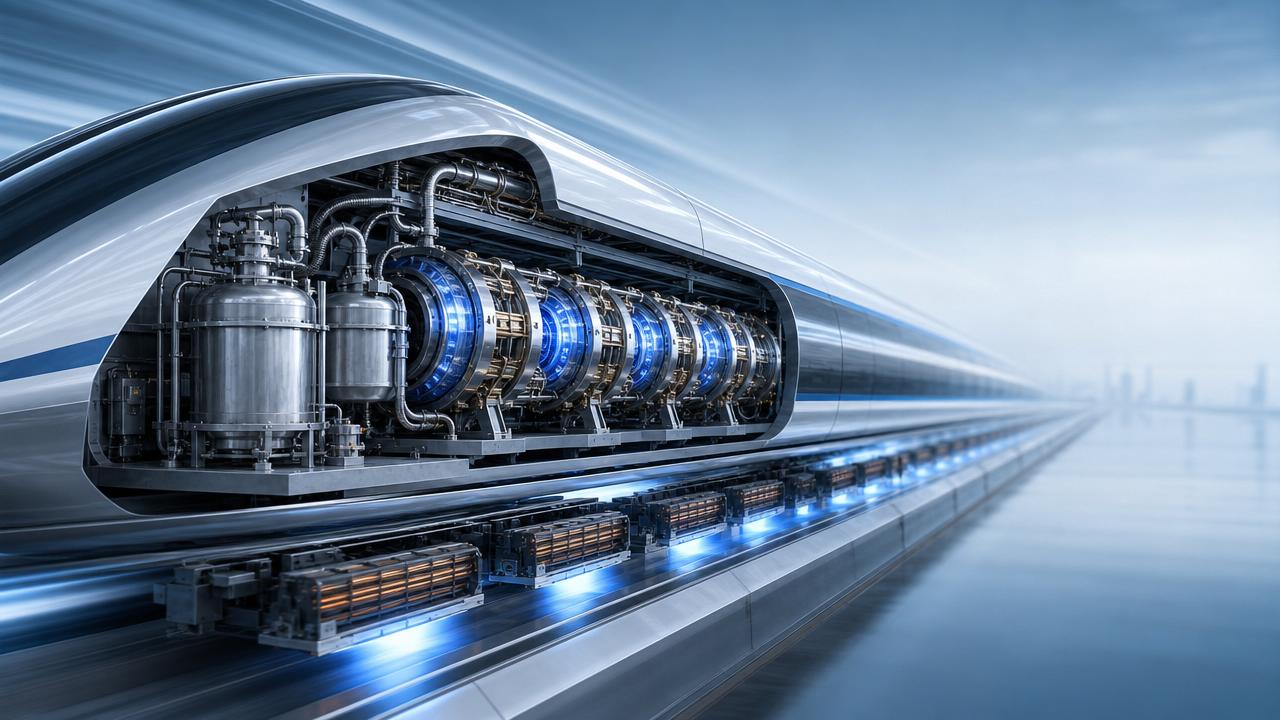
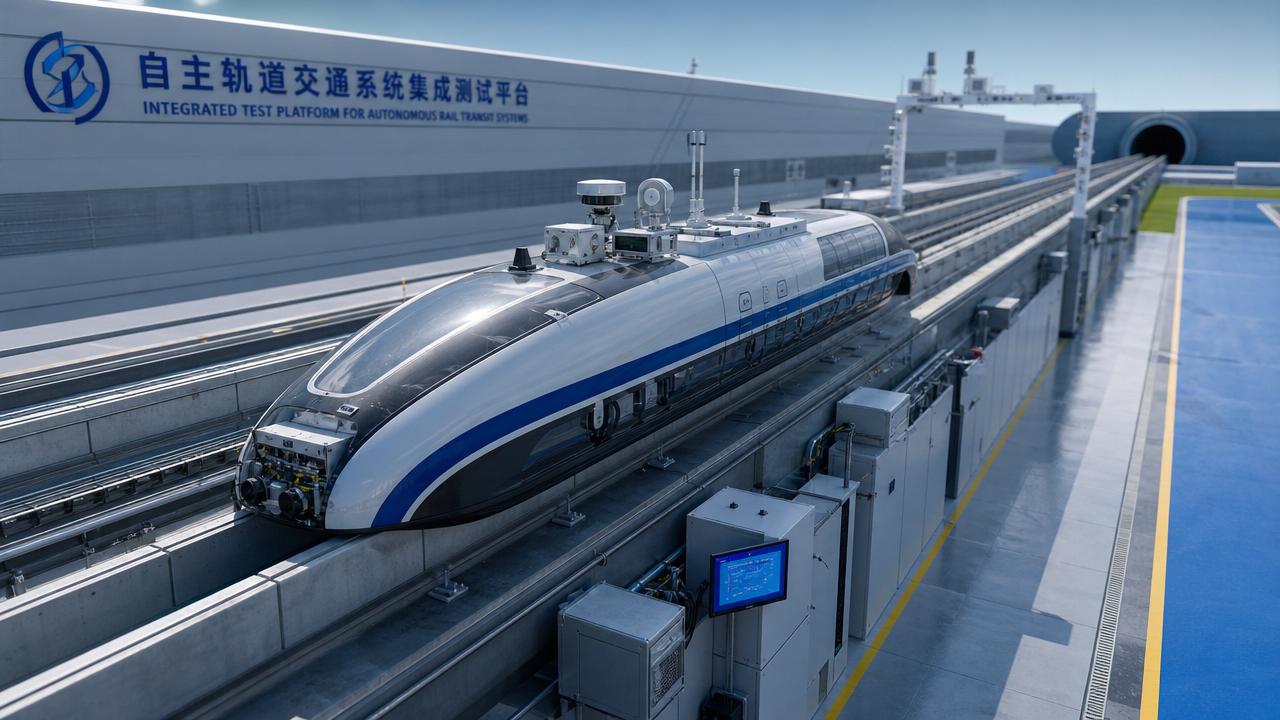
In high-speed rail and maglev environments, the tolerance for delayed recovery is even lower. Small cyber weaknesses can trigger broad timetable and safety consequences.
How should railway cybersecurity controls be prioritized across different rail applications?
Prioritization should follow operational criticality, architecture complexity, and recovery consequences. The right sequence is rarely identical across metro, freight, intercity, and high-speed lines.
This is where institutional benchmarking becomes useful. Comparing architecture and control maturity against standards-led transport sectors reveals where resilience gaps are hidden.
A practical prioritization sequence
- Map critical signaling assets and dependencies.
- Separate networks and remove unnecessary trust paths.
- Control remote access and third-party activity.
- Establish monitoring for OT-specific anomalies.
- Test restore and fallback procedures repeatedly.
How do cost, implementation time, and compliance affect railway cybersecurity decisions?
Cost should be measured against avoided disruption, not tool price alone. A short signaling outage can trigger delay penalties, maintenance overruns, passenger impact, and reputational damage.
The best railway cybersecurity roadmap balances fast wins with engineered upgrades. Some controls are procedural and can start quickly. Others require design review and staged validation.
Typical implementation view
Compliance remains important. Frameworks and sector standards support governance, evidence, and repeatability. Still, compliance should prove resilience, not replace it.
Railway cybersecurity decisions are strongest when they align engineering assurance, operational safety, supplier accountability, and maintainability over the full lifecycle.
What questions should be asked before approving a railway cybersecurity improvement plan?
A useful plan answers operational questions clearly. It should not stop at technology selection.
- Which signaling functions are most time-critical during disruption?
- What single failure or compromise could spread furthest?
- How is third-party access approved, monitored, and revoked?
- Can teams rebuild core configurations within the required recovery window?
- Which controls are validated against live operational constraints?
These questions help separate cosmetic programs from practical railway cybersecurity improvements that truly reduce signaling downtime.
In advanced transportation sectors, resilience comes from disciplined integration. Security controls must fit certified systems, operational rhythms, and long asset lifecycles.
FAQ summary: which railway cybersecurity actions matter first?
Railway cybersecurity is most effective when it is engineered as part of operational continuity, not added as a separate IT layer. The goal is stable signaling, predictable recovery, and controlled system behavior under stress.
The next practical step is to assess critical signaling dependencies, verify access pathways, and test recovery against realistic outage scenarios. That is where measurable downtime reduction begins.
Article Categories
Latest Whitepapers
- 00
0000-00
Aerospace Engineering R&D Facilities: What to Compare Before InvestmentPosted by: Dr. Aris Aero - 00
0000-00
Aerospace R&D Center Locations: How Site Choice Affects CollaborationPosted by: Dr. Aris Aero - 00
0000-00
Transportation Innovation R&D Center Models That Speed Pilot DeploymentPosted by: Marcus Track
SYSTEM_ALERT_URGENT
Q3 SYMPOSIUM ON ORBITAL DYNAMICS
Registration for the Orbital Aerospace technical committee is now open. Node access required.