Railway Cybersecurity Risks Shaping Rail Upgrades in 2026
Lead Author
Published
Views:
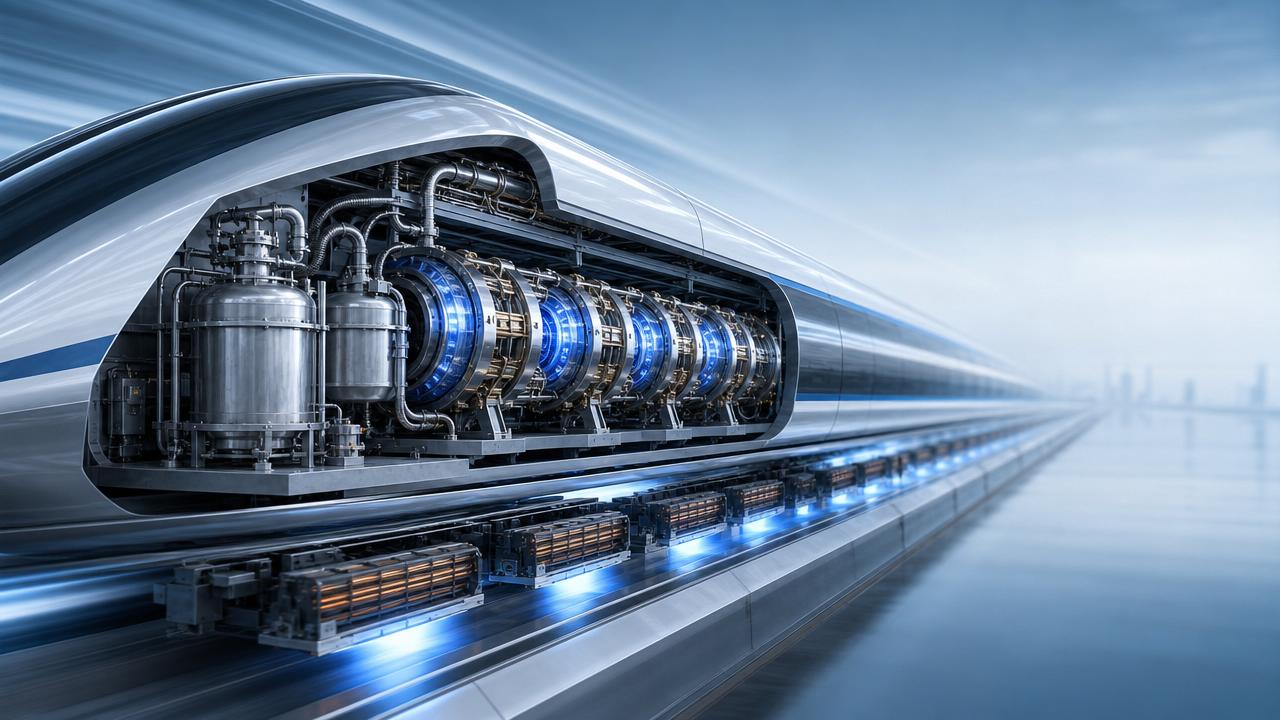
As rail networks become more connected, railway cybersecurity is becoming central to upgrade planning for 2026. Digital signaling, predictive maintenance, edge analytics, and autonomous control improve capacity, but they also widen the attack surface.
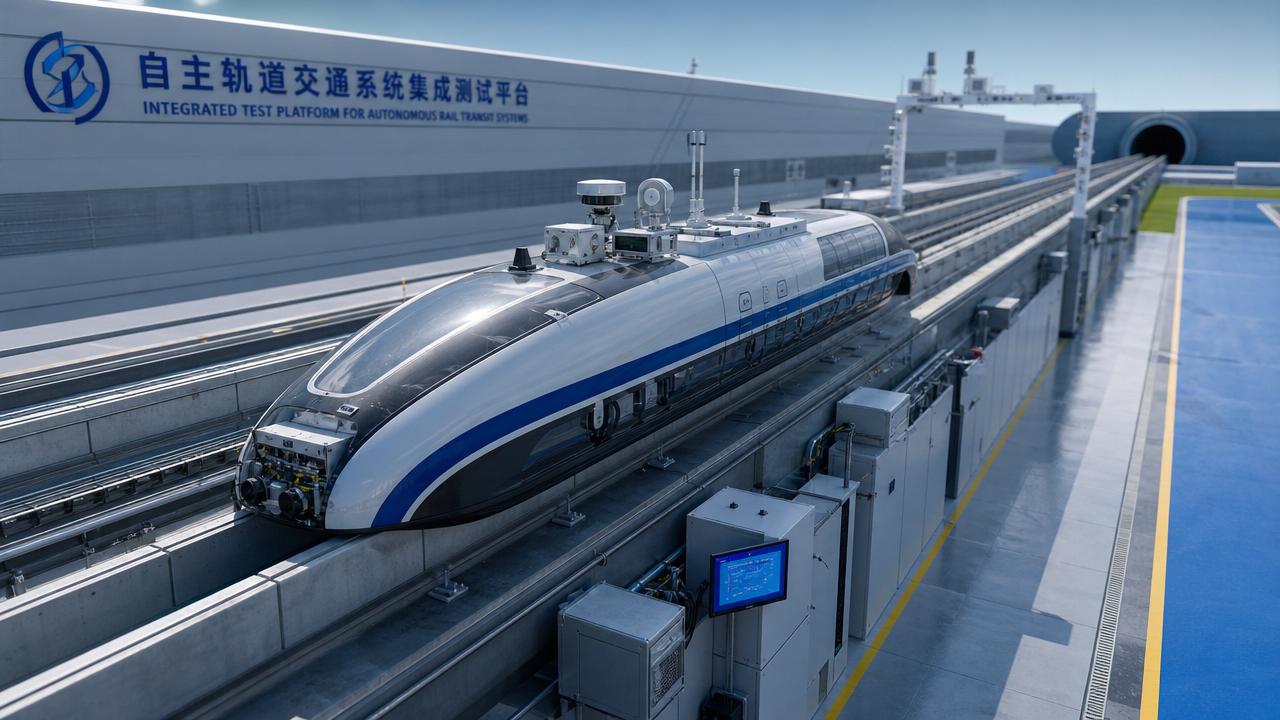
For infrastructure programs tied to high-speed rail, maglev, and cross-border mobility, cyber risk now influences safety cases, procurement strategy, and lifecycle cost. Stronger railway cybersecurity supports resilience, compliance, and investment confidence.
Why is railway cybersecurity shaping rail upgrades in 2026?
Rail upgrades no longer focus only on tracks, power, and rolling stock. They increasingly depend on software-defined operations, connected sensors, cloud-linked diagnostics, and remote maintenance capabilities.

That shift makes railway cybersecurity a board-level engineering issue. A cyber incident can disrupt signaling logic, passenger information systems, dispatching workflows, and freight scheduling at the same time.
In 2026, upgrade decisions are also shaped by geopolitical tension, supply chain digitization, and stricter assurance demands. Rail operators must prove that innovation does not weaken safety or business continuity.
This is especially relevant for advanced transportation ecosystems benchmarked against UIC, ISO, and broader critical infrastructure security expectations. Integrated mobility requires trusted data, authenticated devices, and reliable fallback modes.
- More IP-based signaling and interlocking interfaces
- Greater use of remote monitoring platforms
- Autonomous and semi-autonomous train functions
- Cross-network data exchange with external partners
- Growing dependence on software updates across assets
In practical terms, railway cybersecurity is shaping which upgrades get approved first, which vendors qualify, and how digital transformation roadmaps are sequenced over multiple investment cycles.
Which railway cybersecurity risks matter most for modern rail systems?
The highest-impact risks are those that connect digital compromise with operational disruption. Not every cyber issue creates the same level of safety, revenue, or reputation exposure.
1. Signaling and control system compromise
If attackers manipulate signaling data, route logic, or interlocking communications, operators may need to slow traffic, suspend sections, or switch to restrictive manual procedures.
2. Ransomware affecting operations technology
Ransomware no longer stays within office IT. Poor segmentation can let it affect maintenance servers, depot systems, and interfaces supporting train availability and dispatch readiness.
3. Supply chain and third-party access risk
Rail programs rely on specialist vendors for onboard electronics, telecoms, SCADA, and software support. Weak vendor credentials or insecure remote access can open hidden pathways.
4. Data integrity attacks
Not every attack aims to stop trains. Some alter maintenance records, condition monitoring outputs, or digital twins, leading to poor planning and unsafe asset assumptions.
5. GNSS, wireless, and edge device exposure
As rail systems use more wireless links and location services, spoofing, jamming, and insecure field devices become growing railway cybersecurity concerns for 2026 programs.
How do these risks affect high-speed rail, maglev, and autonomous operations?
The faster and more automated the network, the smaller the tolerance for uncertainty. That is why railway cybersecurity is especially critical in advanced transportation environments.
High-speed rail depends on precise timing, deterministic communications, and safe degradation modes. A cyber disruption may not cause immediate failure, but it can force large operational buffers.
Maglev systems add further complexity through tightly integrated propulsion, guideway monitoring, and centralized control. These architectures require cybersecurity controls aligned with both availability and safety assurance.
Autonomous or driver-assist rail systems rely on sensor fusion, digital maps, software validation, and secure command channels. Any integrity problem can reduce confidence in machine decision-making.
Cross-border corridors face another layer of difficulty. Interoperability between national systems creates exposure around identity management, telecom handoffs, and incident coordination across legal jurisdictions.
- High-speed networks need strong fail-safe communication design
- Maglev programs require secure system-of-systems integration
- Autonomous rail needs trusted software and sensor integrity
- International corridors need harmonized cyber governance
For institutions focused on future mobility, railway cybersecurity is no longer separate from technical benchmarking. It is part of validating whether next-generation transport can scale safely.
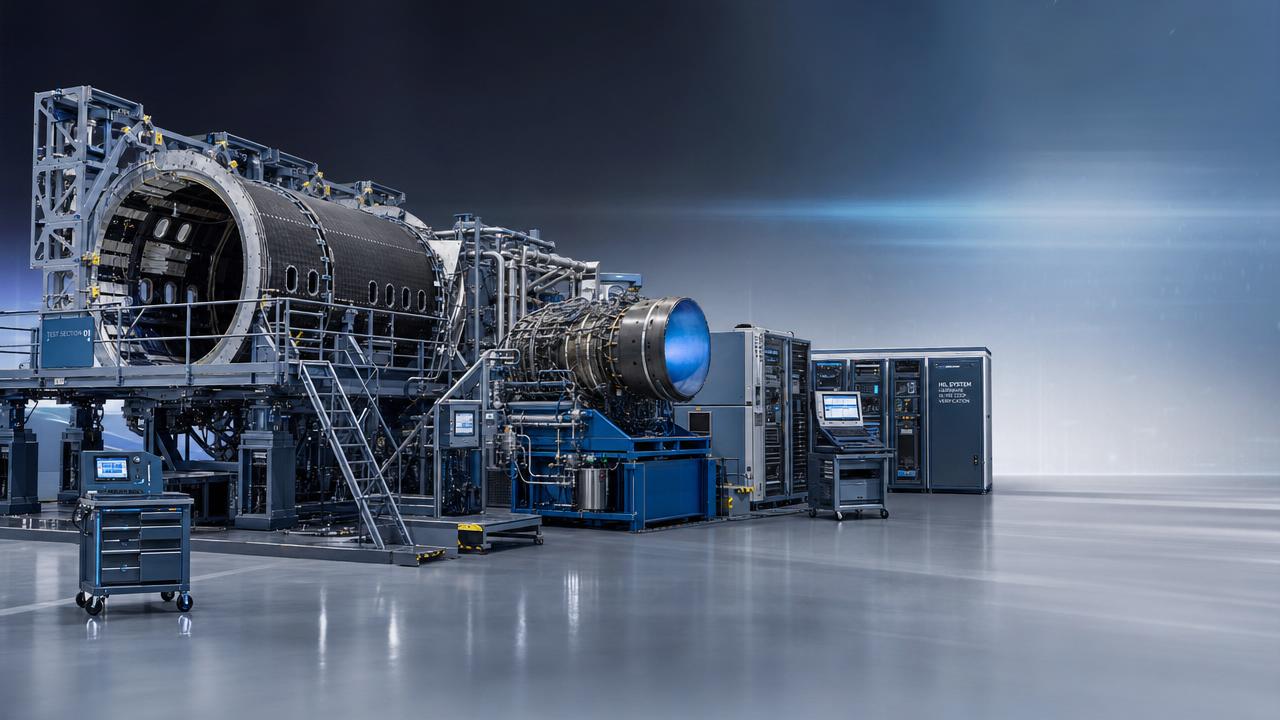
How should organizations judge railway cybersecurity readiness before investing?
A useful starting point is to assess readiness across architecture, governance, supply chain, and recovery capability. Many projects overinvest in tools while underinvesting in engineering discipline.
What to check first
- Map critical assets and safety-linked digital dependencies.
- Separate IT, OT, and safety domains with enforceable controls.
- Review remote access, privileged accounts, and vendor pathways.
- Test backup integrity and operational recovery timelines.
- Align security evidence with certification and assurance needs.
The most mature programs embed railway cybersecurity into procurement specifications, digital engineering models, and acceptance testing. Security should not appear only at commissioning.
Another strong indicator is whether cybersecurity requirements are traceable from concept design to maintenance support. Traceability reduces the gap between policy intent and operational practice.
Decision quality improves when cyber scenarios are tied to business outcomes. Instead of generic scorecards, compare likely disruption hours, safety impact, and cost of degraded operations.
What are the most common mistakes in railway cybersecurity planning?
One common mistake is treating railway cybersecurity as an IT compliance exercise. Rail systems combine legacy equipment, safety functions, and real-time operations that require a different approach.
Another error is assuming isolated systems are automatically secure. Many supposedly isolated assets still receive updates, diagnostics, or contractor access through overlooked connections.
Programs also fail when they ignore asset lifecycle realities. A secure design can weaken over time if patching, configuration control, and spare-part substitution are poorly managed.
Some upgrades focus on detection without recovery planning. In rail, resilience means restoring safe service quickly, with predefined fallback procedures and verified recovery sequences.
What practical actions should guide 2026 rail upgrade strategies?
The best next step is to tie railway cybersecurity directly to upgrade sequencing. Prioritize systems where digital dependence and operational criticality intersect most strongly.
Start with signaling interfaces, operations control centers, remote maintenance channels, and rolling stock software management. These areas often create the greatest network-wide exposure.
Then define measurable requirements for resilience. Examples include recovery time objectives, secure update processes, vendor assurance gates, and evidence for safety-integrated cyber testing.
For complex portfolios, phased deployment is often stronger than full replacement. It reduces disruption while allowing architecture hardening, training, and operational validation in realistic conditions.
In 2026, railway cybersecurity will increasingly determine whether advanced rail investments deliver long-term value. Secure upgrades support performance, protect public trust, and strengthen future mobility readiness.
A practical roadmap should combine engineering review, vendor scrutiny, incident rehearsal, and lifecycle governance. That approach helps rail programs move faster without accepting hidden digital risk.
Article Categories
Latest Whitepapers
- 00
0000-00
Aerospace Engineering R&D Facilities: What to Compare Before InvestmentPosted by: Dr. Aris Aero - 00
0000-00
Aerospace R&D Center Locations: How Site Choice Affects CollaborationPosted by: Dr. Aris Aero - 00
0000-00
Transportation Innovation R&D Center Models That Speed Pilot DeploymentPosted by: Marcus Track
SYSTEM_ALERT_URGENT
Q3 SYMPOSIUM ON ORBITAL DYNAMICS
Registration for the Orbital Aerospace technical committee is now open. Node access required.